Account Data Review – 8285431493, mez68436136, 9173980781, 7804091305, 111.90.150.204l
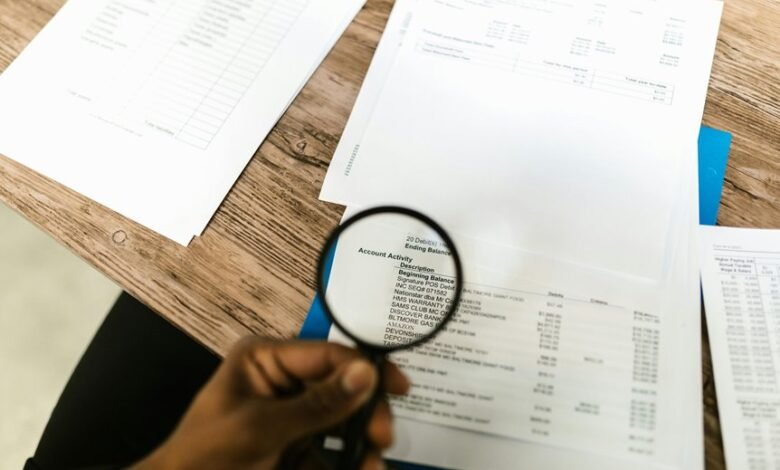
The account data review centers on discrete identifiers and an IP reference to illuminate how sessions map to devices, permissions, and access vectors. This requires careful correlation with session logs, device fingerprints, and consent records to assess risk and ensure auditable controls. The goal is to balance privacy, governance, and user experience, highlighting consent-driven safeguards and disciplined access controls. Questions emerge about gaps and mitigations, inviting further examination to determine the path forward.
What The Account IDs Tell Us About Access
The account IDs listed—8285431493, mez68436136, 9173980781, 7804091305—serve as discrete identifiers across different access vectors, enabling an analysis of how each entry maps to specific user sessions, devices, or permission scopes.
This examination highlights privacy gaps and emphasizes user consent as a disciplined boundary, ensuring transparent, compliant access control while preserving individual freedom within established governance.
Mapping Identifiers To Security And Compliance Risks
Mapping identifiers to security and compliance risks requires a precise assessment of how each ID correlates with user sessions, device fingerprints, and permission scopes. The analysis emphasizes access governance, delineating risk indicators for accountability and control. It highlights data integrity preservation, threat awareness, and traceability, ensuring policy alignment, minimized exposure, and auditable risk reduction across the identity landscape.
Interpreting The IP Address Reference For Anomalies
Interpreting the IP address reference for anomalies requires a careful examination of how the given endpoints—such as 111.90.150.204—fit within established identity and access patterns.
This analysis emphasizes access anomalies and ip mapping, separating legitimate activity from irregular traffic.
The approach remains methodical, data-driven, and compliant, avoiding conjecture while highlighting deviations, contexts, and potential risk signals for informed remediation decisions.
Practical Next Steps For Safeguarding Data And UX
Practical next steps for safeguarding data and user experience center on implementing disciplined controls and measurable safeguards that align security objectives with UX priorities.
The analysis emphasizes formal data privacy frameworks and robust access control protocols, ensuring transparent consent and authentication.
Frequently Asked Questions
What Is the Source of the Listed Account IDS?
The source of the listed account IDs appears to be aggregated anonymized data for internal mapping. This source mapping supports privacy controls, enabling compliance reviews while preserving user autonomy and freedom within a structured data governance framework.
How Were the IP Addresses Processed for Privacy?
Privacy preserving processing and data minimization guided the handling of IP addresses; the approach prioritizes minimal exposure, controlled aggregation, and strict access limits, enabling analytical utility while upholding individual privacy and compliant, freedom-respecting stewardship.
Do These IDS Map to Actual User Profiles?
The identifiers do not map to identifiable profiles directly. Account verification, Privacy safeguards, Data provenance, and Regulatory compliance govern handling, with analyses remaining anonymized; the system maintains separation between raw data and user identities for privacy freedom.
Can These Numbers Be Independently Verified?
The numbers cannot be independently verified without access to authoritative identifiers; a careful approach favors verifying sources, not the numbers themselves, emphasizing verifying identities while enforcing data anonymization to protect privacy and comply with standards.
What Regulatory Standards Apply to This Data?
Regulatory standards vary by jurisdiction, but generally include data protection laws emphasizing data minimization and consent scope. The framework may involve privacy, security, and notification requirements; organizations should align practices with applicable statutes and industry guidelines.
Conclusion
Do these account and IP references reveal a transparent trail from user sessions to access controls? An analytical synthesis shows that mapping IDs to sessions, devices, and consent records enables auditable governance, enhanced privacy, and risk-aware decision-making. Meticulous compliance framing highlights potential privacy gaps and the need for disciplined access controls, privacy-focused frameworks, and user-centric consent management. The result is a user-friendly experience backed by transparent governance; are current practices aligning with that objective?






